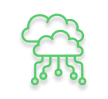
Imagine this: It’s a Tuesday morning in your Midtown or Brooklyn clinic. Patients are waiting, charts need pulling, and suddenly every screen locks up with a ransom note.
Your EHR is frozen. Phones are ringing off the hook. And the panic sets in – “Is patient data gone? How long will we be down? What about HIPAA?”
Unfortunately, this isn’t hypothetical anymore. Ransomware attacks on healthcare have surged, and NYC medical practices are squarely in the crosshairs. As someone who’s helped dozens of practices in New York recover from these nightmares, we can tell you one thing for sure: what you do in the first few hours makes all the difference.
Here’s a clear, step-by-step ransomware response plan for healthcare providers in NYC. The plan offers a strong focus on HIPAA compliance after ransomware attack and getting you back to caring for patients as safely and quickly as possible.
1. Why Ransomware Hits NYC Medical Practices So Hard
Healthcare remains one of the most targeted sectors for a simple reason: patient data is incredibly valuable on the dark web, and practices often run on legacy systems with limited IT resources.
In recent years, ransomware attacks on healthcare have continued to climb sharply. According to the 2025 Verizon Data Breach Investigations Report , the healthcare sector experienced 1,710 security incidents, with 1,542 confirmed data disclosures – many involving ransomware. Healthcare remains the most targeted industry, accounting for 22% of all ransomware attacks across sectors (Black Fog, 2025). A single successful attack on a medical practice or hospital system can mean:
- Days or weeks of downtime
- Risk of exposed protected health information (PHI)
- Major HIPAA violations and potential fines
- Lost revenue and damaged patient trust
For NYC practices juggling tight schedules, regulatory demands, and real patient care, the stakes are even higher. One prolonged outage doesn’t just hurt your bottom line; it can delay critical care.
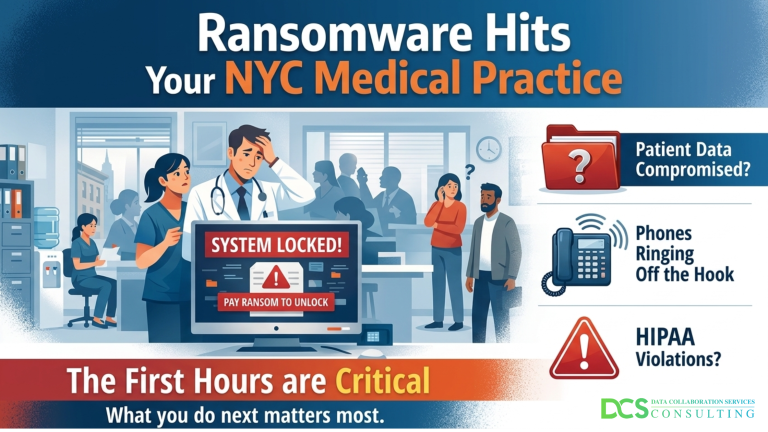
2. Contain the Attack (Do This First)
What to do after a ransomware attack? The moment you suspect ransomware, stop the bleeding.
- Immediately disconnect infected devices from the network (unplug Ethernet cables or disable Wi-Fi). Do not power them off yet, this can destroy valuable forensic evidence your team or investigators will need.
- Isolate any shared drives, servers, or cloud resources that might be connected.
- Preserve evidence: Take screenshots of the ransom note and note the exact time the attack was noticed.
Goal: Prevent the malware from spreading further while you activate your response.
3. Activate Your Response Plan
Don’t wing it. Every medical practice should have a documented ransomware response plan for healthcare and everyone on staff should know where to find it (paper copy recommended).
- Contact your IT/security team or managed SOC provider right away (ideally someone who already knows your environment).
- Notify key internal stakeholders: practice administrator, compliance officer, and leadership.
- Document everything: Which systems are affected, what you observed, who you contacted, and when.
If you don’t have a formal plan yet, this is your wake-up call. Fast, coordinated action limits damage and strengthens your HIPAA compliance after ransomware attack position.
For a deeper dive into HIPAA requirements, see our guide: Understanding HIPAA Compliance: The Ultimate Guide |
4. Assess the HIPAA Impact
Ransomware doesn’t always equal a reportable breach, but you must investigate thoroughly.
- Determine whether protected health information (PHI) was accessed, exfiltrated, or encrypted.
- Work with your IT team and legal counsel to conduct a risk assessment: Was the data properly encrypted and unreadable? What exactly was impacted?
- If a breach occurred, you have strict HIPAA notification timelines (usually 60 days to affected individuals and HHS).
HIPAA compliance after ransomware attack is non-negotiable. Proper documentation and a thorough investigation can sometimes mean the difference between a reportable breach and a contained incident.
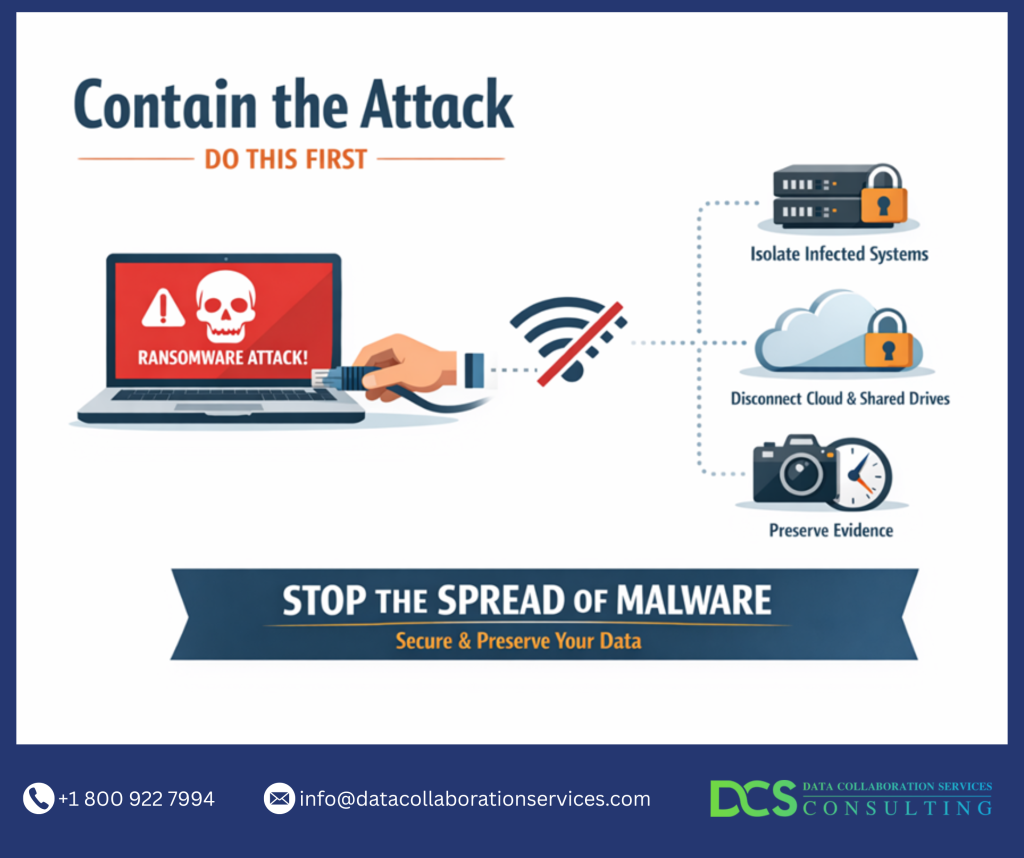
5. Restore and Secure
This is where many practices stumble – rushing to get systems back online without cleaning the environment first.
- Recover only from clean, verified backups (ideally immutable/offline backups that the ransomware couldn’t touch).
- Rebuild or restore systems on a clean network segment first.
- Reset all passwords and access credentials.
- Patch vulnerabilities, update software, and strengthen security controls (MFA everywhere, better segmentation, endpoint protection).
- Test everything thoroughly before bringing systems back into production.
Prioritize critical systems first – patient scheduling, EHR access, billing, and emergency protocols.
Many practices we help now aim for the 72-hour recovery target that’s becoming a de facto standard for serious compliance and cyber insurance requirements.
See How: we helped a New York Clinic Achieve HIPAA Compliance and Strengthen Healthcare Data Security |
The Bottom Line for NYC Healthcare Practices
A ransomware attack is terrifying, but a fast, well-executed response can dramatically reduce the damage – to your patients, your reputation, and your finances.
What to do after a ransomware attack comes down to preparation, speed, and expertise. This is exactly why partnering with the right NYC healthcare cybersecurity expert matters.
At Data Collaboration Services, we help medical practices across New York develop practical ransomware response plans, implement strong backups, and maintain HIPAA compliance after ransomware attack. We’ve guided practices through containment, recovery, and the road back to normal operations – often faster and with less disruption than they expected.
If you’re a medical practice in NYC (or anywhere in the Northeast) and want to make sure you’re truly prepared or if you’re currently dealing with an incident, reach out to us. We offer no-pressure assessments and practical guidance tailored to healthcare environments.
Don’t fall for the bait. Get help now. Book a free cybersecurity and recovery consultation for your practice today. Call (800) 922-7994 or visit datacollaborationservices.com
Your patients and your team are counting on you to be ready.