The Threat Is Real – and It’s Targeting New York Businesses.
It’s a Wednesday morning in your Midtown Manhattan office. The phones are ringing, your team is logging in and then, one by one, every screen locks up. A ransom note appears. Files encrypted. Operations frozen. A countdown clock ticking.
This isn’t a hypothetical. This is the reality of a ransomware extortion attempt and for thousands of New York businesses each year, it’s becoming a real nightmare. New York’s dense concentration of financial firms, law offices, healthcare providers, and small and mid-sized businesses makes it one of the most attractive targets in the country. The United States alone accounts for 47% of global ransomware attacks (Varonis, 2026) and a disproportionate share hits right here in the Northeast.
When the attack hits, there’s one question that dominates everything else in that chaotic moment: Do we pay the ransom?
The answer is: almost never. This guide is here to cut through the panic, give you a clear framework, and help you make the right call.
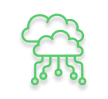
Step 1: Assess the Situation – Don’t Panic, Act
The first minutes of a New York business ransomware attack are the most critical. Panic leads to mistakes and mistakes lead to bigger damage. Here’s what you need to do immediately:
- Identify and isolate impacted systems: Disconnect infected devices from your network – unplug Ethernet cables, disable Wi‑Fi, and isolate shared drives or servers. Do not power the machines off. Shutting down can destroy forensic evidence that your IT team will need to trace the attack’s entry point.
- Preserve the evidence: Take screenshots of the ransom note. Document the exact time you noticed the attack. Note which systems are affected and in what sequence.
- Contact your IT security team immediately: If you work with a managed security provider or a Managed SOC service provider, call them first. Speed matters more than almost anything else in the first hour.
- Notify internal stakeholders: Loop in your leadership, legal counsel, and compliance officers. If customer data may be compromised, your legal team needs to be in the loop early.
One of the most common mistakes businesses make is trying to handle this internally without expert help. A seasoned cybersecurity responder can often assess the scope of an attack, determine whether data was exfiltrated, and chart a recovery path far faster than an untrained internal team operating under stress.
Here’s what you need to do in the first 72 hours after a ransomware attack
Step 2: Understand the Risks of Paying – The Numbers Might Surprise You
Every business facing a ransomware extortion attempt eventually confronts the central dilemma: should you pay ransomware attackers, or not? Cybersecurity experts and law enforcement officials almost universally advise against paying and the data backs them up.

Paying doesn’t buy you safety.
Here’s what the research tells us about why paying is so risky:
- There’s no guarantee your data comes back intact
Even after paying, many businesses discover they’ve lost data permanently. Only 46% of ransom payers recovered their data successfully, and often with corrupted or incomplete files. Sophisticated ransomware groups today operate with a double-extortion model, they encrypt your data and steal it. Even if you get the decryption key, they still hold your data over you.
- You signal to attackers that you’re a payer
The cybercriminal underground is a highly networked community. When a business pays, that information circulates. Cybersecurity experts have warned that once an organization pays, it may be viewed as a more attractive target for future attacks. Rather than closing the door, payment can leave it wide open with a welcome mat.
- Legal and compliance exposure is real
Depending on your industry and the nature of the attack, paying a ransom may trigger regulatory reporting obligations. In some cases, particularly if the ransomware group is on a U.S. government sanctions list, paying could even constitute a legal violation. For New York businesses in regulated industries like finance or healthcare, this layer of exposure deserves serious legal counsel before any payment decision is made.
- The cost of paying is just one part of the total bill
The average cost of recovery from a ransomware attack reached $1.53 million in 2025 and that figure excludes the ransom itself (Sophos, 2025). Businesses that pay the ransom still face investigation costs, remediation, downtime, legal fees, and reputational damage. The ransom is the beginning of the financial pain, not the end.
None of this means payment is never considered – in some extreme cases, with no viable backup and mission-critical data at stake, the calculus may shift. But it should be the last resort, made with legal and cybersecurity counsel involved, not a panicked first response.
Step 3: Focus on Recovery – This Is How You Actually Win
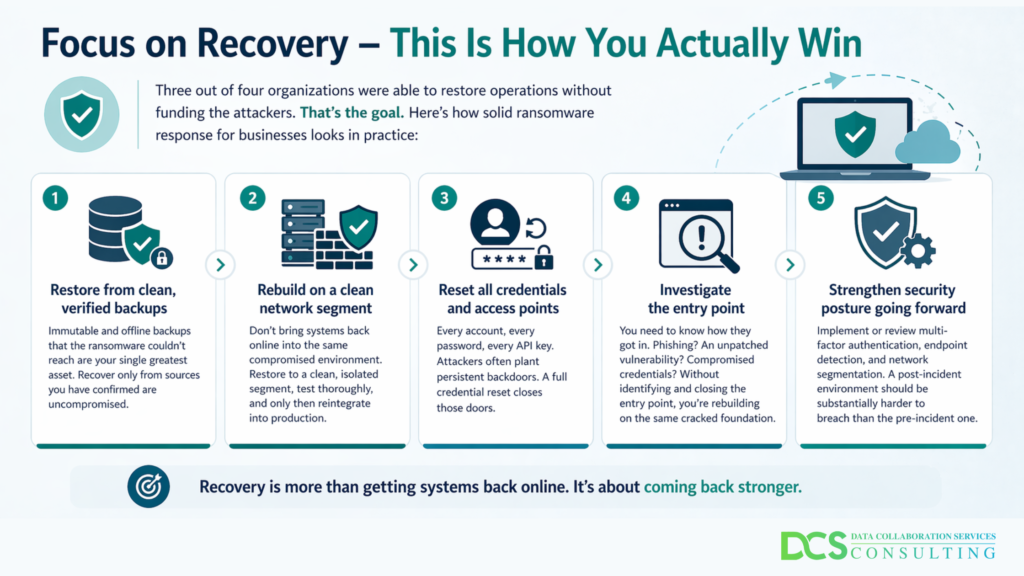
The smarter question isn’t “should you pay ransomware” attackers – it’s “how do you recover without paying?”
In Q4 2024, only 25% of ransomware victims paid the ransom – an all-time low (Coveware via Deepstrike, 2025). The primary reason? Improved backup strategies. Three out of four organizations were able to restore operations without funding the attackers. That’s the goal. Here’s how solid ransomware response for businesses looks in practice:
- Restore from clean, verified backups: Immutable and offline backups that the ransomware couldn’t reach are your single greatest asset. Recover only from sources you have confirmed are uncompromised. DCS’s Data Backup & Recovery services are built exactly for this, providing immutable backups, multi-factor authentication, and encrypted storage specifically designed to withstand ransomware.
- Rebuild on a clean network segment: Don’t bring systems back online into the same compromised environment. Restore to a clean, isolated segment, test thoroughly, and only then reintegrate into production.
- Reset all credentials and access points: Every account, every password, every API key. Attackers often plant persistent backdoors. A full credential reset closes those doors.
- Investigate the entry point: You need to know how they got in. Phishing? An unpatched vulnerability? Compromised credentials? Without identifying and closing the entry point, you’re rebuilding on the same cracked foundation.
- Strengthen security posture going forward: Implement or review multi-factor authentication, endpoint detection, and network segmentation. A post-incident environment should be substantially harder to breach than the pre-incident one.
Also worth reading:
From Phishing to Ransomware: The Cybersecurity Guide Every Business Needs

Businesses aiming for a 72-hour recovery window are increasingly meeting it – but only when they have both a tested incident response plan and reliable backups already in place. How to survive a ransomware attack comes down to preparation made long before any ransom note ever appears on your screen.
The Bottom Line: Fast Action Matters More Than Panicked Payments
A ransomware extortion attempt is designed to be terrifying. The countdown clock, the threatening language, the loss of access to everything – it’s deliberate psychological pressure engineered to make you act irrationally. Don’t let it work.
For New York businesses, the right response to a New York business ransomware attack is a disciplined, expert-led process: isolate, assess, consult, recover. Businesses that recovered from these attacks with the least damage are not the ones that paid the fastest – they’re the ones that had a plan, had proper backups, and had a trusted cybersecurity partner in New York they could call the moment things went haywire.
At Data Collaboration Services (DCS), we work with small and mid-sized businesses across New York City and the Northeast to help strengthen their security posture and infrastructure without cutting a check to cybercriminals. Whether you’re in the middle of an incident right now, or want to make sure you never land in those troubled waters, we’re here to help.
Don’t wait for a ransom note to find out if you’re ready. Book a free cybersecurity consultation with the DCS team today or call (800) 922-7994.